The Web is a wild place, with more than the NSA potentially out to get you. With the so-called six strikes antipiracy initiative in full effect, you never know if Hollywood is monitoring your peer-to-peer activity. Then there are the malicious hackers trying to reset email, Facebook, and Twitter passwords.
No security regimen short of complete hermitage can keep you 100 percent secure. Nevertheless, you can take a few simple precautions to maintain your privacy online and deter all but the most determined bad guys.
Secure the line
One of the worst online security mistakes you can make is to connect to an email, bank, or other sensitive account over public Wi-Fi. If that’s unavoidable—because you spend a lot of time in cafés, hotels, or airports, for example—paying for access to a virtual private network can significantly improve your privacy on public networks.
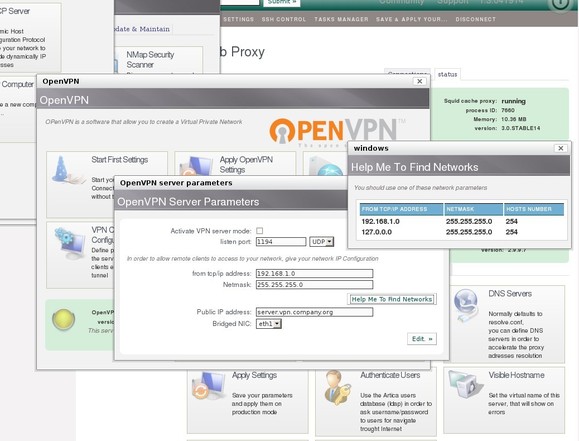
VPNs serve as an encrypted tunnel that prevents bad guys from getting between you and the Internet in order to steal your login credentials or other sensitive information.
You can use a free virtual private network client like OpenVPN to connect to a VPN service where you have an account, so you can browse the Web through an encrypted tunnel.
That’s a great reason to use a VPN, but it’s not the only one. Maybe you don’t want your Internet service provider to monitor your online activity at home. Normally when you connect online, your ISP can observe all of your activity. Over a VPN, however, your ISP can see only your connection to the VPN. As a bonus, many VPNs can help you bypass region blocks for sites like Amazon, Hulu, Netflix, and BBC’s iPlayer.
Not all service providers are created equal, however. Some VPN services log all of your browsing activity, thereby negating the point of using a VPN for privacy.
Stop leaving private data in the cloud
Online file-syncing services such as Dropbox, Google Drive, and SkyDrive are among the best innovations to grace the Internet. But while the convenience of viewing your latest photos on Dropbox or of pulling text documents from iCloud may be fantastic, much of your data sits unencrypted on those company servers.
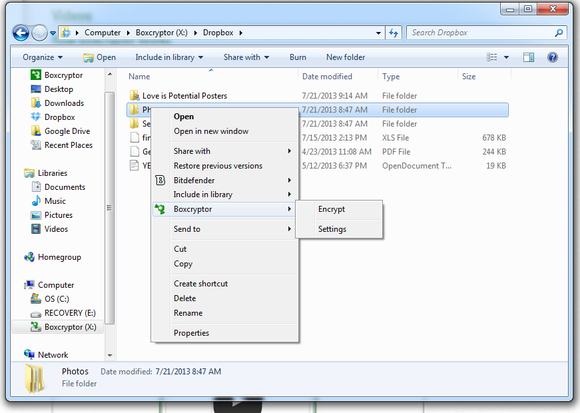
That means your data is available to law enforcement officials who obtain the right paperwork, regardless of how little objective justification they have for looking at your stuff. And any well-informed hacker can break into your account by using social engineering techniques, by discovering weaknesses in a company’s server security, or by conducting a brute-force attack that tries to guess your password.
For sensitive data that you need to sync across devices, a better alternative is to use an encrypted cloud storage service. You can build one yourself by encrypting data on your PC before sending it to Dropbox, using free software such as BoxCryptor or the open-source TrueCrypt.
You can use a file encryption utility like BoxCryptor to encrypt files before storing them on remote storage services like Dropbox.
A far simpler method, however, is to find a file-syncing service that offers built-in storage encryption.
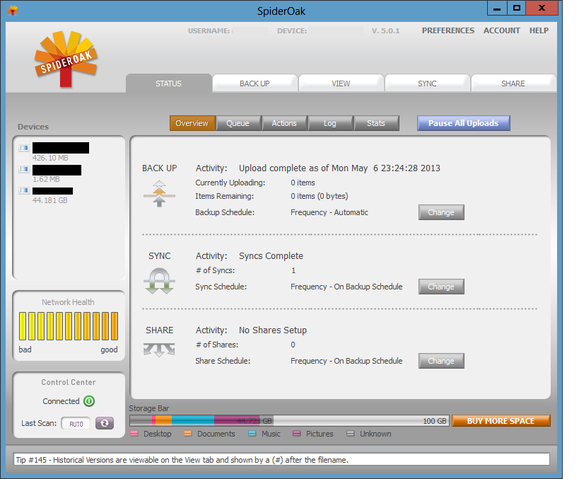
Two popular encrypted storage services are SpiderOak and Wuala (pronounced like voilà). Both services bill themselves as “zero-knowledge solutions,” meaning that they don’t know what you’re storing on their servers—and that they have almost no way of knowing, even if they wanted to. When you use SpiderOak, for example, the password you choose is factored into the encryption keys generated by the SpiderOak client. The only way for anyone, even a SpiderOak employee, to access your files—short of a quantum computer or a lucky guess—is by inputting your password. Password-building best practices dictate you should choose a phrase of at least ten characters that consists of an assortment of letters, numbers, and symbols.
The downside of services like SpiderOak and Wuala is that if you forget your password, you’re pretty much out of luck. Both companies say they have no way of retrieving your password and can provide only a password hint that you entered during the signup process.
Despite the tight standard security, you can access your data on both services in a less secure way. If you log into your SpiderOak account from the company’s website or from a mobile device, your password gets stored in encrypted memory for the duration of your session. This is the only situation, SpiderOak says, where your data might be read by someone with access to its servers. For maximum privacy, you should access your files only via the SpiderOak desktop client.
Use SpiderOak’s desktop client for maximum security
Wuala claims to encrypt and decrypt your data on a mobile device similar to the way it handles the task on your PC. But when you share folders from Wuala using a Web link, the encryption key gets included in the URL. So anyone who receives the URL can view the contents of that folder, and the key has to be sent to Wuala’s servers for decryption. Wuala claims its service “forgets” the key after decryption, but that’s still one instance where using Wuala is less secure.
SpiderOak, based in Illinois, offers 2GB of free online storage, which should be enough for the mission-critical documents you need to sync across devices. If your storage needs are larger, try Switzerland-based Wuala, which offers 5GB free.
Both services provide back-up and Dropbox-like functionality. SpiderOak’s Hive sync sits on your PC as a special folder, while Wuala syncs to your PC as a network drive.
As is true of any online secure service, you have to be comfortable with the company and trust that the service is doing what it claims it is to keep your data secure.
Secure your online services with two-factor authentication
The first line of defense for keeping your online services secure is to use unique, random, passwords of ten characters or more for every account you have—just don’t forget to store them in a good password manager. For even better security, turn on two-factor authentication for Google, Facebook, and every other service that offers it.
Two-factor authentication requires you to enter a short numeric code in addition to your password before you can gain access to your account. The code usually comes from a physical fob or from a smartphone application. The good news is that you can get most of your two-factor authentication codes from Google’s Authenticator app for Android and iOS.
Authenticator automatically works with accounts such as Dropbox, Evernote, Google, LastPass, and Microsoft. Facebook offers its own code generator inside the social network’s mobile app, but you can add Facebook to Authenticator as well. From the Facebook newsfeed, click the settings cog in the upper right corner and select Account Settings.

On the next page, click Security in the left-hand navigation column. Under ‘Security Settings’ look for the ‘Code Generator’ menu option and click Edit to the far right of that option.
Click the link in the first two words of the sentence Set up another way to get security codes.
A QR code should appear in a pop-up window. Open Authenticator, navigate to the ‘Add Entry’ option, select Scan Barcode, and point your phone’s camera at the QR code on your monitor. In a few seconds, your phone will identify your Facebook account code and add it to Authenticator. Enter a Facebook code from Authenticator to ensure that everything’s working properly, and you’re done.
Two-factor authentication isn’t foolproof, but it does add a hurdle to help deter anyone who wants to get into your account. Twitter offers its own two-factor authentication, but its method is not compatible with Google’s Authenticator. The last time we checked, Twitter’s authentication method still had some kinks to work out.
If two-factor authentication isn’t enough security for you, take stock of the backup email address you use for all of your online accounts. Consider using one or several unique email addresses as password recovery addresses. Just make sure that you never give out these email addresses for personal mail and that they aren’t similar to your other accounts.
VPNs, encrypted storage, and two-factor authentication are great tools for keeping your data secure and your online activity as private as possible. They may sometimes be a bit of a pain to work with—especially when you’re entering extra codes in Authenticator. But dealing with a minor headache now is a lot easier than enduring the major migraine you’ll feel if you let yourself get hacked when you could have stopped the bad guys in their tracks.
Source: PCworld.com
 iTechBahrain Information Technology Digital Marketing Web & Mobile Development Services
iTechBahrain Information Technology Digital Marketing Web & Mobile Development Services